Open Temp Mail Inbox
Open temp mail inbox services provide instant, disposable email addresses for signing up on websites, receiving verification codes, and avoiding spam in your primary inbox. These tools are free, require no registration, and automatically delete messages after a short period. By using a temporary inbox, you safeguard your personal email from phishing, data breaches, and unwanted marketing, making it essential for digital privacy in today’s online world.
Key Takeaways
- Instant Access: You can open a temp mail inbox in seconds without creating an account or providing personal information.
- Privacy Shield: It acts as a barrier between your real identity and potentially risky online platforms, preventing spam and data harvesting.
- Automatic Cleanup: Inboxes and their contents are automatically deleted after a set time (usually 1-24 hours), ensuring no digital footprint remains.
- Verification Essential: It’s the perfect tool for receiving one-time verification links or codes for social media, forums, or app downloads.
- Not for Critical Accounts: Never use a temp mail inbox for important accounts like banking, primary email recovery, or legal documents, as you will lose access permanently.
- Simple & Free: These services are completely free to use, with a straightforward interface focused on speed and anonymity.
- Limited Functionality: Temp mail is for receiving only; you typically cannot send emails from these addresses.
📑 Table of Contents
- What Exactly is a “Temp Mail Inbox”?
- How to Open and Use a Temp Mail Inbox: A Step-by-Step Guide
- Primary Use Cases: Why You Should Open a Temp Mail Inbox
- The Security and Privacy Implications: What You Gain and What You Don’t
- Limitations and Pitfalls: What Can Go Wrong?
- Best Practices for Responsible Temp Mail Usage
- The Future of Disposable Email: Where Are We Headed?
- Conclusion: Your Digital Paper Shredder for Email
What Exactly is a “Temp Mail Inbox”?
Imagine you need to download a free ebook, but the website demands your email address. You hesitate, knowing this might lead to a flooded inbox with promotional newsletters. This is where the magic of a temp mail inbox comes in. At its core, a temporary email service generates a random, disposable email address for you to use on a whim. You “open” this inbox on the service’s website, use the provided address wherever needed, and then close the browser tab. The inbox exists only for a fleeting moment—often just an hour or a day—before self-destructing along with all its messages.
Think of it like a burner phone for your email. You get a number (the email address) for a short-term, specific job (signing up for a contest, accessing a gated article) and then discard it. The primary goal is anonymity and inbox hygiene. Your permanent, personal email address remains pristine, associated only with your trusted contacts and essential services. The technology behind it is simple: the service provider maintains a pool of email domains and randomly assigns an address from that pool to your session. All incoming mail for that address is routed to a temporary database linked to your browser session, accessible only to you via the unique inbox URL.
The Core Philosophy: Privacy by Ephemerality
The fundamental principle is ephemerality—the idea that data doesn’t need to persist to be useful. In an era where every online action is tracked, stored, and analyzed, a temp mail inbox offers a deliberate return to impermanence. It rejects the “data is the new oil” mentality for low-stakes interactions. You are not building a long-term identity with this address; you are performing a single transaction and moving on. This philosophy directly counters the default model of most web services, which is to collect and retain your email as a key asset for marketing and user profiling.
How to Open and Use a Temp Mail Inbox: A Step-by-Step Guide
Using a temporary email service is designed to be absurdly simple, often requiring fewer clicks than ordering a coffee. The entire process from arrival to having a usable address typically takes under 10 seconds. Here’s a practical walkthrough.
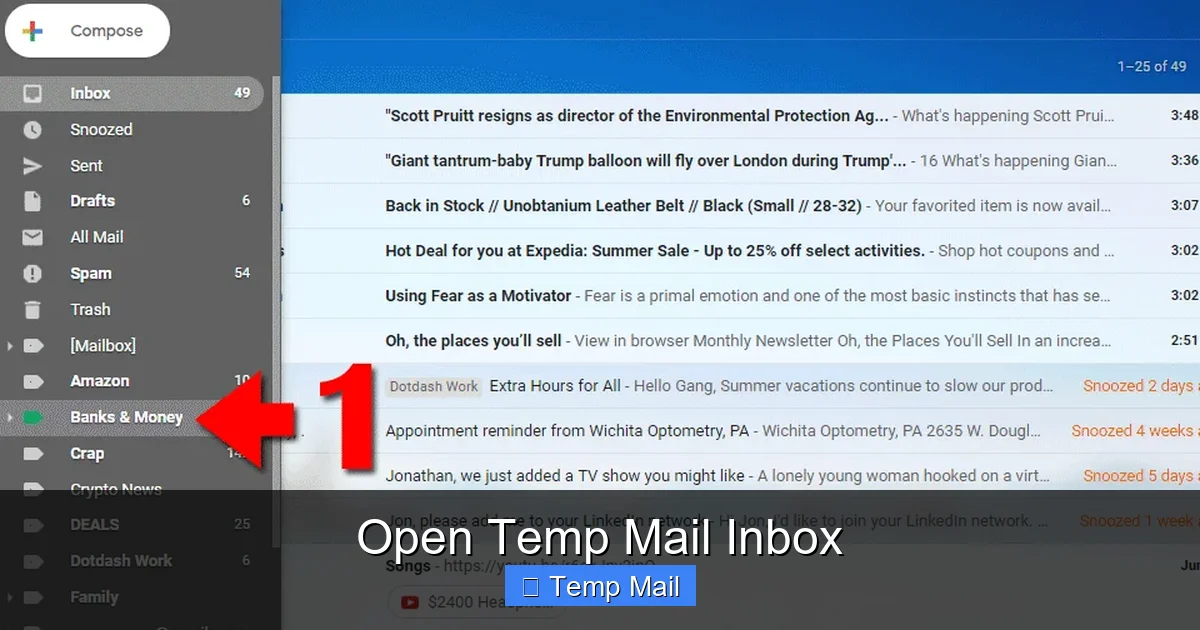
Visual guide about Open Temp Mail Inbox
Image source: docucopies.com
Step 1: Navigate to a Reputable Service
Open your web browser and go to a well-known temp mail site like Temp-Mail.org, 10MinuteMail.com, or Guerrilla Mail. You’ll land on a homepage that is refreshingly bare—no “Sign Up” or “Log In” buttons cluttering the view. The focus is on the inbox itself.
Step 2: Your Inbox is Already Open
Yes, really. Upon loading the page, a random email address is already generated for you and displayed prominently at the top of the page. Below it, you’ll see an empty inbox window. You have already opened a temp mail inbox. The service has created a unique session for your browser, linking that address to your view.
Step 3: Copy and Use the Address
Click the “Copy” button next to the email address. Now, paste it into any website’s sign-up or download form that requests an email. Proceed with the process. When the site sends a verification email, it will appear in your temporary inbox window, often within seconds.
Step 4: Refresh and Retrieve
If the email doesn’t appear immediately, hit the “Refresh” button (usually a circular arrow icon) in the inbox panel. This manually checks the server for new messages. Click on the message subject to open it and find the verification link or code. Copy the code or click the link (be cautious with links from untrusted sites).
Step 5: Close and Forget
Once you’ve retrieved what you needed, simply close the browser tab. Your work is done. You do not need to log out or delete anything. After the service’s predetermined time limit (often displayed as a countdown timer), the inbox and its address will be automatically purged from the system, making it available for another user. There is no trace left on your end.
Pro Tip: Some services allow you to manually choose your temporary address from a list of domains or even create a custom username. If you need a specific address for a recurring but non-critical task (like a weekly newsletter you don’t trust), look for this feature. However, remember it’s still temporary and not permanent storage.
Primary Use Cases: Why You Should Open a Temp Mail Inbox
Understanding when to use a disposable email is as important as knowing how. These use cases highlight the practical value of keeping your primary email sacred.
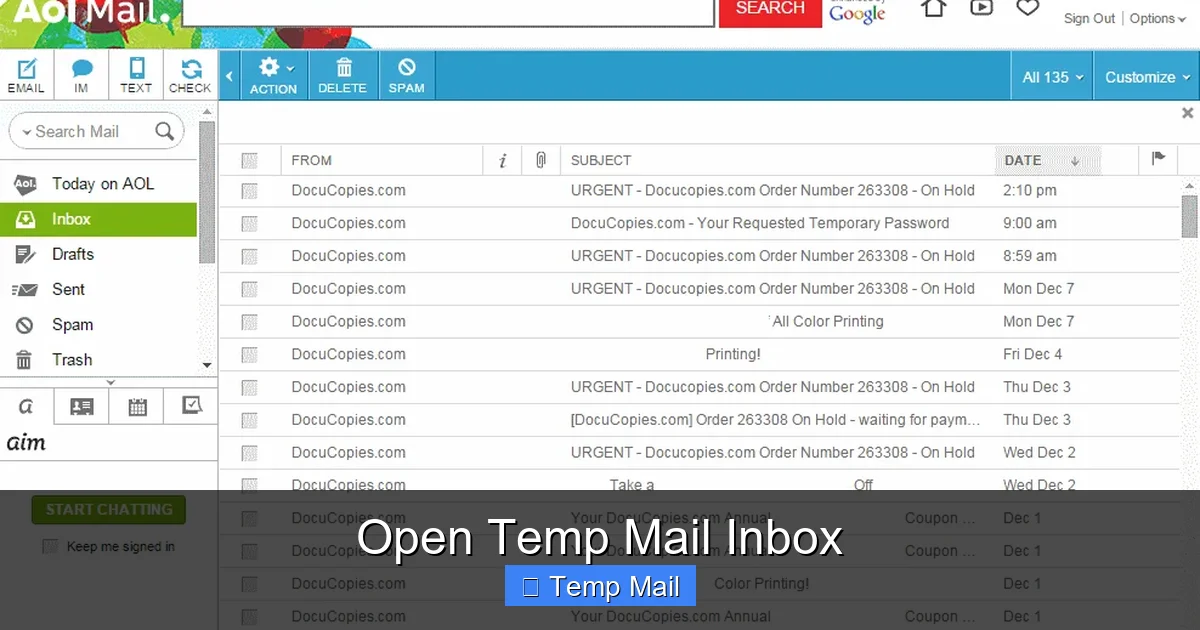
Visual guide about Open Temp Mail Inbox
Image source: i.ytimg.com
1. Bypassing Gated Content and Download Walls
How many times have you wanted to read an industry report, download a software trial, or access a whitepaper, only to be stopped by an email gate? Using your real email here often results in being added to a sales drip campaign that lasts months. A temp mail inbox is the perfect key. You get the immediate content you wanted, and the vendor gets an address that will bounce their next promotional email, effectively opting you out without any effort.
2. Safe Account Creation on Low-Trust Platforms
You’re joining a new forum, a gaming server, or a comment-heavy news site. You have no long-term intention of maintaining this identity or trust in the platform’s security practices. Using your primary email risks a data breach exposing it to spammers or worse. A temporary address isolates that risk. If the platform suffers a breach, only the disposable address is compromised, leaving your main accounts untouched.
3. Avoiding Spam from One-Time Purchases
You’re buying a single item from an unfamiliar online store. The checkout requires an email for order confirmation. Providing your main email almost guarantees your address will be sold to third-party advertisers or added to the store’s relentless promotional list. A temp mail address gets you the receipt (if you need it) and then vanishes, breaking the spam chain at the source.
4. Testing and Development
For software developers, QA testers, or marketers setting up email automation flows, temp mail is a godsend. You can quickly create multiple inboxes to test how a signup form, a password reset email, or a notification sequence works without polluting your real inbox or managing dozens of fake permanent accounts. It’s a lightweight tool for validation.
5. Protecting Identity on Anonymous Platforms
Individuals researching sensitive topics, whistleblowers, activists in oppressive regions, or simply someone wanting to post candid feedback on a workplace review site without professional repercussions can use a temp mail to create an anonymous account. The unlinkable nature of the address adds a layer of operational security.
The Security and Privacy Implications: What You Gain and What You Don’t
A common misconception is that a temp mail inbox is a “secure” or “encrypted” communication tool. This is mostly false. Understanding its true privacy profile is crucial.
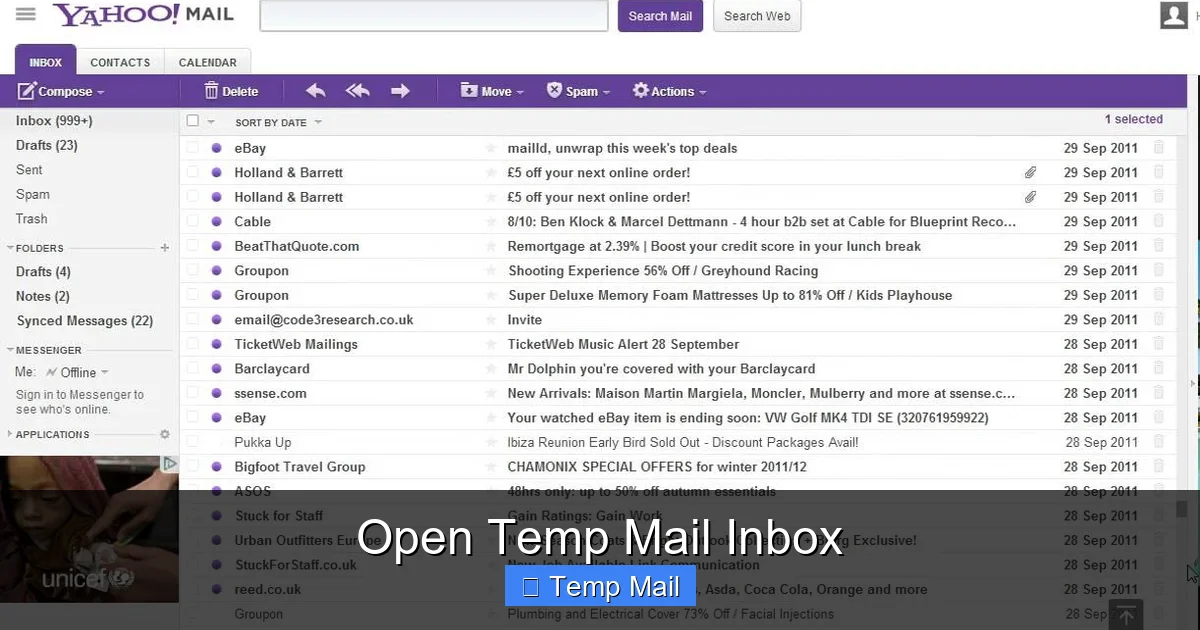
Visual guide about Open Temp Mail Inbox
Image source: i.ytimg.com
The Privacy Gain: Separation and Anonymity
The primary privacy benefit is separation. You prevent cross-site tracking via your email address. Ad networks and data brokers often use your email as a unique identifier to stitch your activity across hundreds of websites. By using a different, disposable address for each new site, you break that linkage chain. The anonymity comes from the fact that no personal information (name, phone, etc.) is required to open the inbox. The address is not tied to your identity in any database the service keeps, because the service doesn’t keep a persistent database linking you to that address beyond your active session.
The Security Reality: Not for Sensitive Data
It is vital to understand that the communication is not end-to-end encrypted. The email is stored in plain text on the temp mail provider’s servers during its short lifespan. A malicious actor hacking that provider’s server could, in theory, read all active temporary emails. Therefore, you should never use a temp mail address for:
- Password recovery for your main email or bank account.
- Receiving confidential documents like contracts, tax forms, or medical records.
- Any communication where the content itself is sensitive and could cause harm if intercepted.
The security model is based on transience, not encryption. The assumption is that the window for compromise is so short (the inbox lives for 1 hour) that the risk is acceptable for low-sensitivity tasks. The threat model is about avoiding spam and data aggregation, not state-level adversaries.
Can the Service Operator See My Emails?
Technically, yes. Anyone operating the temp mail service can see the emails that pass through their system. This is why it’s critical to use reputable, well-established services with transparent privacy policies (even if short-lived). Look for services that explicitly state they do not log IP addresses, do not require cookies for basic operation, and purge data aggressively. While you trust them with your low-stakes emails, you are still placing a degree of trust in the operator. For the highest anonymity, some advanced users route their browser through a VPN or Tor network before accessing a temp mail service.
Limitations and Pitfalls: What Can Go Wrong?
No tool is perfect, and temp mail has clear boundaries. Knowing these limitations prevents frustration and potential lock-outs.
The Vanishing Act: You Lose Access Permanently
This is the most critical limitation. Once the inbox expires, the address is gone forever. There is no password recovery, no “forgot inbox ID” link. If you need to reset a password on a service you signed up with using a temp mail, you are locked out permanently. The service’s “account” is tied to the disposable address, which no longer exists. This is why the cardinal rule is: Never use temp mail for any account you might need to access long-term.
Blocked by Some Services
Many major platforms (Google, Facebook, Twitter, Microsoft, most financial institutions) actively block known disposable email domains. They maintain lists and reject them at the sign-up stage to prevent fraud and abuse. If you try to use a temp mail on these sites, you’ll likely get an error message saying the email is invalid. This is a feature, not a bug, from their perspective. It means temp mail is best suited for smaller websites, forums, and content platforms with less rigorous checks.
Delayed or Missing Emails
Sometimes, an expected verification email might not arrive. This can be due to the sending website’s server rejecting the temp domain, a delay in the temp mail service’s polling system, or the email being caught in a spam filter on the sender’s side. Always have a backup plan. If a critical service (like a utility bill payment portal) won’t accept a temp mail, you’ll have to use your real address.
Limited Features
Do not expect a full-featured email client. There is typically no folder organization, no search across multiple messages (if you get more than one), no attachments handling (some may block attachments entirely), and certainly no calendar or contact management. It’s a bare-bones, single-purpose inbox.
Best Practices for Responsible Temp Mail Usage
To get the most value and avoid headaches, follow these guidelines.
- Use it for the Intended Purpose Only: Stick to sign-ups, verifications, and content access. Never try to use it for personal correspondence or business communication.
- Check the Timer: Most interfaces show a countdown. If you need more time, some services offer a one-click “Extend” button to add time to your current inbox. Use this sparingly, as the point is brevity.
- Don’t Refresh Excessively: Constantly hitting refresh won’t make emails arrive faster and may trigger anti-abuse mechanisms on some services. Be patient; give it 30-60 seconds.
- Clear Your Browser Data After: For maximum privacy, close the tab and clear your browser’s session data (cookies and cache) for that temp mail site. This severs any lingering connection between your browser and that specific inbox session.
- Have a Primary Inbox Ready: Always keep your real, primary email address accessible. If a crucial service absolutely requires a verified, permanent email, you must use your real one. Temp mail is a supplement, not a total replacement.
- Choose a Service with a Good Reputation: Stick to popular, long-standing services. A shady temp mail site could itself be a phishing front, designed to capture the very credentials you’re trying to protect. Look for clean interfaces, clear countdowns, and no aggressive ads that mimic site buttons.
The Future of Disposable Email: Where Are We Headed?
As online privacy concerns mount, the demand for tools like the temp mail inbox will likely grow. We may see evolution in a few directions. First, integration with privacy-focused browsers and password managers. Imagine your browser’s autofill automatically suggesting a new disposable address from a built-in provider when you hit an email field. Second, more robust APIs for developers to implement disposable email acceptance on their own sites, creating a more standardized ecosystem. Finally, there could be a shift towards “semi-permanent” masks—aliases that last for a week or a month, offering a bit more flexibility for recurring but non-essential subscriptions, while still being easy to revoke. The core concept, however, will remain: providing a simple, instant way to say “no” to permanent email exposure for trivial tasks.
Conclusion: Your Digital Paper Shredder for Email
Learning to open a temp mail inbox is a fundamental digital literacy skill in the 21st century. It’s the online equivalent of using a paper shredder for junk mail or giving a fake number at a noisy bar. It’s a small, deliberate act of reclaiming control over your digital identity. By consistently using a disposable address for the myriad of low-stakes, high-noise sign-ups that define modern web browsing, you perform a kind of digital hygiene. You keep your primary email—your most important online asset—clean, secure, and reserved for human connections and critical services. The tool is simple, free, and powerful. Used wisely, it’s an indispensable part of a privacy-conscious toolkit, turning the tide against the relentless collection of your data, one temporary inbox at a time.
Frequently Asked Questions
Is using a temp mail inbox legal?
Yes, using a temporary email service is perfectly legal. It is simply a tool for receiving email without using your personal address. The legality depends on how you use it; using it for fraud, illegal activities, or to circumvent bans is illegal, but using it for privacy protection is not.
Can I send emails from a temp mail inbox?
Almost never. Temporary email services are designed almost exclusively for receiving messages. The ability to send is typically disabled to prevent spam and abuse. If you need to send an email anonymously, you would need to look for a different anonymous email service, not a standard temp mail provider.
How long does a temp mail inbox last?
It varies by provider, but common timeframes are 10 minutes, 1 hour, or 24 hours. The countdown timer is always displayed on the service’s page. Once the time expires, the inbox and its address are permanently deleted and cannot be recovered.
Will websites know I’m using a temp mail address?
Yes, easily. The domain name (the part after the @) will be from a known disposable email provider. Many websites check for these domains and may block sign-ups from them to reduce fake accounts and fraud. If a site rejects your temp mail, you’ll need to use a different address.
Is my activity on a temp mail site tracked?
It depends on the provider’s policy. Reputable services claim not to log IP addresses or store session data beyond the active inbox lifetime. However, the site itself can see your IP address when you visit. For maximum anonymity, access the temp mail site through a VPN or the Tor network.
What happens if I need to reset a password for an account I signed up with using temp mail?
You will be permanently locked out of that account. Password reset links are sent to the registered email address, which no longer exists after the inbox expires. This is why the golden rule is to never use a temporary email for any account you might need to access in the future, especially for important services.