Anonymous Email
An anonymous email is a message sent without revealing your real identity or personal information to the recipient. It uses specialized services or techniques to mask your IP address, hide your true email address, and prevent tracking. While invaluable for privacy, security, and avoiding spam, it requires careful use to avoid legal issues and ensure effectiveness. This guide covers everything from how it works to choosing the right tool for your needs.
Imagine you need to sign up for a forum to research a sensitive topic. Or you want to tip a journalist about corporate misconduct without fear of retaliation. Maybe you’re just tired of your primary inbox being bombarded with promotional spam after every online purchase. In these scenarios and countless others, a standard email address tied to your name and phone number becomes a liability. This is where the concept of an anonymous email enters the picture—a powerful, often misunderstood tool for reclaiming digital privacy.
But what does “anonymous email” really mean? Is it truly untraceable? Is it legal? And with so many services claiming to offer privacy, how do you choose the right one without wasting time or compromising your security? This guide will cut through the noise. We’ll explore the mechanics, the legitimate use cases, the significant risks, and provide a clear framework for using anonymous email effectively and responsibly. Think of this as your complete owner’s manual for private digital correspondence.
Key Takeaways
- Core Purpose: Anonymous email primarily severs the link between your online activity and your real-world identity, protecting personal information from data harvesters, spammers, and surveillance.
- Two Main Types: They generally fall into “temporary/disposable” emails for quick, one-time sign-ups and “secure/encrypted” anonymous email services for more sustained, private communication.
- Not Absolute Anonymity: True anonymity requires a holistic approach—using anonymous email alone is insufficient without practices like using a VPN, Tor browser, and avoiding personal details in the message body.
- Legal & Ethical Boundaries: Using anonymous email for illegal activities (fraud, harassment, threats) is still illegal. Anonymity is a tool for privacy, not a shield for crime.
- Provider Trust is Crucial: You must trust your anonymous email provider. A malicious or compromised provider can log your activity, defeat the purpose, and potentially hand over your data.
- Limited Functionality: Many anonymous email services block attachments, have sending limits, and may not support rich formatting, as these features can be vectors for tracking or abuse.
- Recipient Perspective: Emails from anonymous services often land in spam folders. Recipients may be wary of or outright block emails from known anonymous domains.
📑 Table of Contents
- How Does Anonymous Email Actually Work?
- Legitimate and Critical Use Cases for Anonymous Email
- The Significant Risks and Pitfalls You Must Know
- How to Choose the Right Anonymous Email Service
- Legal and Ethical Boundaries: Where Anonymity Ends
- The Future of Anonymous Communication and Practical Tips
- Conclusion: Anonymity as a Mindset, Not Just a Tool
How Does Anonymous Email Actually Work?
At its core, an anonymous email service works by interposing a layer between you and the recipient. It prevents the standard email headers—which contain your IP address, device information, and the path the email took—from being attached or makes them meaningless. The method varies significantly depending on the type of service you use.
The Disposable/Temporary Email Model
This is the most common form people encounter. Services like Temp-Mail, 10MinuteMail, or Guerrilla Mail generate a random, public email address (e.g., xyz123@tempmail.com) that anyone can access via a web interface for a short period (10 minutes to 24 hours).
- Process: You visit the site, a new inbox is created for you. You copy that address, use it to sign up somewhere, then return to the site to view the confirmation email. The inbox and address are automatically deleted after the timer expires.
- Anonymity Level: Low to medium. The service itself doesn’t require any registration, so there’s no account linking you to the address. However, your IP address is visible to the service provider when you access the inbox. If the provider keeps logs (many do, briefly), that connection exists. The recipient only sees the temporary domain, not your IP.
- Best For: One-time sign-ups, downloading a file that requires an email, bypassing a paywall that asks for an email. Not for any ongoing conversation.
The Secure/Encrypted Anonymous Provider Model
Services like ProtonMail, Tutanota, or Mailfence are designed from the ground up for privacy. They often require no personal information for sign-up and operate from privacy-friendly jurisdictions.
- Process: You create an account (often with just a username and password). These services use end-to-end encryption, meaning even they cannot read the content of your emails. They strip identifying metadata from headers and route traffic through their own infrastructure.
- Anonymity Level: Medium to high. To maximize anonymity, you must sign up without using identifying information and access your account via a VPN or Tor. The recipient sees your @protonmail.com address, but there is no inherent link to your real identity unless you put it in the message body.
- Best For: Journalist-source communication, activist coordination, long-term private correspondence where you control the address.
The Technical “Mix” or “Remailer” Approach
This is a more technical, old-school method. A chain of servers (remailers) strips the original sender’s information and re-adds the message, making tracing extremely difficult. Modern tools like the Tor network can achieve a similar effect for webmail access.
- Process: You send an email through a specialized client that routes it through multiple anonymizing nodes before it reaches the final destination.
- Anonymity Level: Very high, but complex to set up correctly for average users. Misconfiguration can break the anonymity chain.
- Best For: Technically sophisticated users with a high threat model (e.g., whistleblowers in oppressive regimes). Not recommended for casual use.
Legitimate and Critical Use Cases for Anonymous Email
Understanding why you might need an anonymous email is as important as knowing how to get one. The motivations are rooted in fundamental privacy rights and practical security.
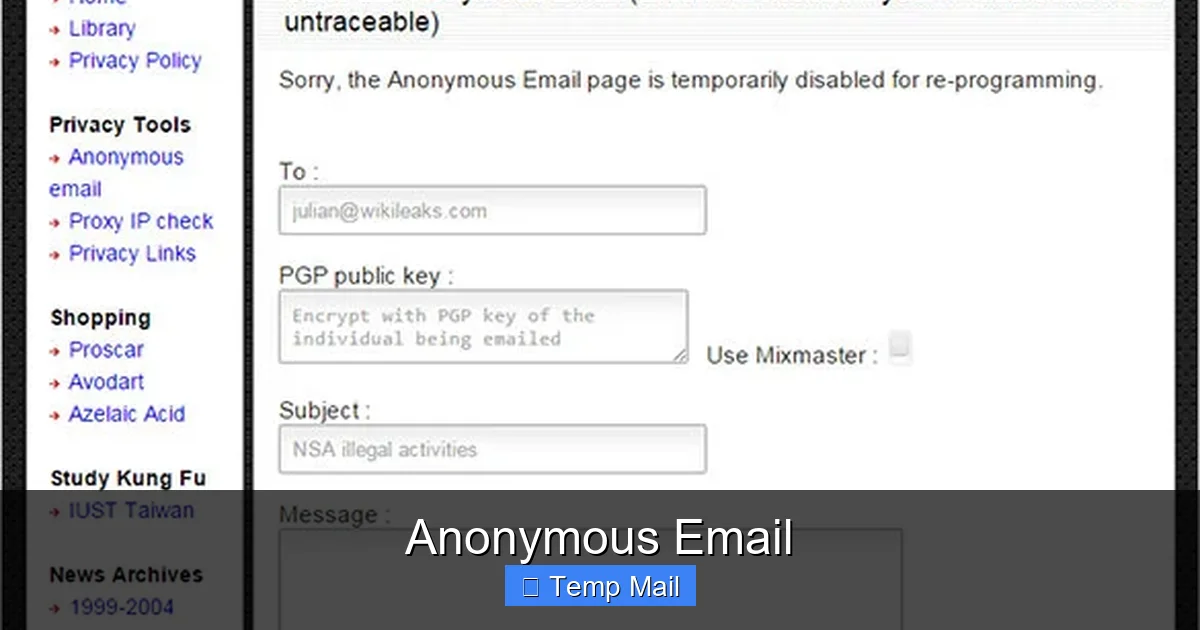
Visual guide about Anonymous Email
Image source: images.template.net
Protecting Personal Privacy from Data Harvesting
Every time you use your primary email for a newsletter, a store loyalty program, or a free app download, you are feeding the data broker ecosystem. These entities compile detailed profiles on you. Using a disposable or anonymous email for these low-stakes interactions creates a dead-end for data harvesters. The profile they build is attached to a throwaway address that expires, not to your real identity. This is a simple, powerful way to limit the commercial surveillance that defines modern internet life.
Security Research and Threat Intelligence
Security professionals, bug bounty hunters, and researchers often need to interact with potentially malicious websites, phishing kits, or threat actor infrastructure. Using a real email would instantly link their identity (and employer) to their investigation. An anonymous email allows them to gather intelligence, sign up to observe criminal forums, or receive phishing samples without becoming a target themselves. It’s a standard operational security (OpSec) practice in the infosec community.
Journalism and Whistleblowing
This is one of the most vital use cases. Sources with sensitive information about government corruption, corporate malfeasance, or public health risks must communicate without fear of being identified through their digital footprint. Secure providers like ProtonMail are explicitly designed with this in mind, offering features like zero-access encryption and anonymous sign-up. The infamous platform SecureDrop often integrates with such services to facilitate this exact process, allowing sources to upload documents and communicate via an anonymous email portal.
Bypassing Censorship and Repressive Regimes
In countries with heavy internet censorship, citizens and activists use tools like Tor to access blocked information. Often, creating accounts on necessary services (like a forum for organizing or a news site) requires an email. Using a global, anonymous email provider that isn’t blocked by the state firewall is a critical step in maintaining access to uncensored information and organizing safely.
Avoiding Spam and Unwanted Marketing
This is the everyday, practical use. You want to download a whitepaper or enter a contest. You know providing your main email will result in years of spam. A temporary address solves this perfectly. The confirmation email comes in, you click the link, and the address vanishes. No clutter, no long-term data linkage.
The Significant Risks and Pitfalls You Must Know
An anonymous email is a tool, and like any tool, it can be misused or fail due to poor handling. Understanding the risks is non-negotiable for using it safely.
Visual guide about Anonymous Email
Image source: images.template.net
False Sense of Security: The “I’m Invisible” Fallacy
This is the biggest danger. Users often think that by using a temporary address, they are completely untraceable. This is rarely true. Your anonymity chain is only as strong as its weakest link:
- Your IP Address: If you access your anonymous inbox from your home internet without a VPN, the email provider (and potentially the recipient if headers are preserved) can see your real IP, which is easily linked to your ISP and physical location.
- Browser Fingerprinting: Even on a temporary site, your browser’s unique configuration (fonts, plugins, screen size) can be used to track you across sessions if the provider employs tracking scripts (some less-scrupulous disposable services do).
- Message Content: You could be using a perfectly anonymous service, but if you write “Hi, this is John from 123 Main Street” in the email body, you have instantly de-anonymized yourself. Metadata within attached documents (EXIF data in photos, document properties in PDFs) can also reveal information.
Legal Consequences and Jurisdictional Nightmares
Anonymity does not equal illegality, but it attracts scrutiny. Law enforcement can and does obtain logs from email providers through legal requests (subpoenas, warrants). The key question is: what logs does the provider keep?
- Logging Policies: Reputable secure providers (ProtonMail) are based in strong privacy jurisdictions (Switzerland) and have court-tested policies against voluntary data sharing. Many disposable services, however, are run by entities in less-regulated countries and may log IPs and timestamps for “abuse prevention,” creating a paper trail.
- Illegal Activity: Sending threats, fraud, defamation, or copyright-infringing material via an anonymous email is still a crime. Anonymity may delay identification, but it is not a permanent shield. Providers will cooperate with valid international legal requests for serious crimes.
Service Reliability and Trust Issues
You are placing immense trust in your anonymous email provider.
- Shutdowns and Seizures: Disposable services can disappear overnight. If you’re relying on one for important account recovery, you could be locked out permanently.
- Malicious Providers: Some “free anonymous email” sites are honeypots, explicitly designed to log all activity and IPs to sell to advertisers or hand over to authorities. Others may inject ads or malware into your session.
- Lack of Support: If you lose access to a temporary inbox, there is zero customer support to recover it. Your data is gone.
Technical and Deliverability Problems
From a purely practical standpoint, anonymous emails face an uphill battle.
- Spam Filters: Domains used by temporary and anonymous services are notorious for spam. Your email is highly likely to be flagged and sent directly to the recipient’s spam folder, or even blocked entirely by their email provider.
- No Sender Reputation: These domains have no sending history, no SPF/DKIM/DMARC records (security protocols), making them look incredibly suspicious to modern spam filters.
- Feature Poverty: Don’t expect to send large attachments, use rich formatting, or integrate with calendars and contacts. These features require more infrastructure and create more potential privacy leaks.
How to Choose the Right Anonymous Email Service
Not all anonymous email services are created equal. Your choice depends entirely on your threat model and use case. Ask yourself: What am I protecting against? A spammer? A corporation? A government?

Visual guide about Anonymous Email
Image source: images.template.net
For Quick, One-Time Tasks: Disposable Email
If your goal is simply to avoid spam for a single sign-up:
- Look For: No registration required, HTTPS encryption (padlock icon), clear expiration policy (e.g., “emails deleted after 1 hour”), and a simple, clean interface without aggressive ad placements.
- Red Flags: Sites that ask for any personal details to “generate” an address, excessive pop-up ads, or unclear data retention policies.
- Recommended Practice: Use a well-known, reputable service like Temp-Mail or 10MinuteMail. Bookmark it. Never use the same disposable address twice for important accounts.
For Sustained Private Communication: Secure Email Providers
If you need a reliable address for ongoing private conversations:
- Jurisdiction is Key: Choose a provider based in a country with strong privacy laws and outside the Five/Nine/Fourteen Eyes intelligence alliances (e.g., Switzerland, Germany, Iceland). This provides a higher legal barrier to data requests.
- Open Source & Audited: Providers like ProtonMail and Tutanota have open-source code that can be independently verified for security flaws and backdoors. Look for independent security audits.
- Zero-Access Encryption: Ensure the provider uses end-to-end encryption where even they cannot read your emails. Tutanota encrypts the entire mailbox; ProtonMail encrypts messages between its users and offers PGP support.
- Anonymous Sign-Up: The best services allow sign-up with just a username and password, no phone number verification.
The Non-Negotiable Companion: A VPN
Regardless of the email service you choose, your internet connection is the first point of exposure. Your Internet Service Provider (ISP) can see every site you visit, including your anonymous email provider’s website. Using a reputable, no-logs VPN is the single most important step to enhance the anonymity of any email activity. It encrypts your traffic and masks your real IP address from the email service you’re accessing. For the highest threat model, combine this with the Tor Browser.
Legal and Ethical Boundaries: Where Anonymity Ends
It is a critical misconception that an anonymous email places you above the law. It does not. Understanding the legal landscape is essential for responsible use.
What is Legal?
Using anonymous email is, in itself, legal in virtually all democratic countries. The act of protecting your privacy is a right. Legitimate activities include:
- Signing up for a website without using your real name.
- Communicating with a therapist or support group anonymously.
- Submitting a tip to a crime reporting hotline.
- Researching sensitive or controversial topics without creating a searchable link to your identity.
What is Illegal?
The legality is determined by the content and intent of the communication, not the tool used. Using an anonymous email to commit a crime does not make the crime legal. Common illegal uses include:
- Harassment & Threats: Sending threatening, abusive, or stalking messages.
- Fraud & Phishing: Impersonating someone else to defraud them or steal credentials.
- Copyright Infringement: Sending pirated content en masse.
- Defamation: Publishing false statements that damage a person’s reputation.
- Soliciting Illegal Acts: Planning or coordinating violence, terrorism, or drug trafficking.
The “Crime-Fraud” Exception
This is a key legal doctrine. If law enforcement can demonstrate to a judge that an anonymous communication was used to further a crime or fraud, they can obtain a court order compelling the email provider to produce any logs or information they have. A provider’s promise of anonymity typically has this exception baked into its Terms of Service. They will fight overly broad requests, but they must comply with valid, specific legal demands for serious criminal activity.
The Future of Anonymous Communication and Practical Tips
The landscape of digital privacy is constantly evolving. As governments push for “traceable” anonymity (e.g., mandatory sender verification for bulk email) and AI improves traffic analysis, the tools for private communication must adapt.
Emerging Trends
- Decentralized & Blockchain-Based Email: Projects like Mailchain or services built on blockchain aim to create email-like communication that is inherently decentralized and resistant to single-point compromise or seizure.
- Improved Metadata Protection: Future secure email protocols will likely focus even more aggressively on stripping or encrypting all metadata (who sent what to whom and when), which is often more revealing than content.
- Integration with Privacy Ecosystems: Expect tighter integration between secure email providers, VPNs, and privacy-focused browsers, offering bundled “privacy suites” for the average user.
Your Actionable Checklist for Safe Use
Before you send your next anonymous email, run through this mental checklist:
- Define Your Threat Model: Are you avoiding spam, a data broker, an employer, or a government? Your answer dictates the tool.
- Use a VPN First: Always activate your VPN before opening your anonymous email provider’s website.
- Use a Privacy-Focused Browser: Use Firefox with strict privacy settings or the Tor Browser. Disable JavaScript if possible (though it may break some webmail interfaces).
- Never Re-Use Addresses: A disposable address is for one task. A secure anonymous address should be used for a specific purpose (e.g., “activism@protonmail.com”) and not for your online shopping.
- Scrub Your Message: Do not include your name, location, phone number, or any personally identifiable information in the body or subject line. Be mindful of context (e.g., “See you at the doctor’s office tomorrow” reveals a lot).
- Assume It’s Not 100%: For high-stakes situations, assume there is a theoretical possibility of compromise. Plan accordingly. Use encrypted messaging apps (Signal) for real-time chat instead of email where possible.
- Research the Provider: Read their privacy policy. Where are they based? What is their logging policy? Have they been audited? Have they ever been compelled to hand over data?
Conclusion: Anonymity as a Mindset, Not Just a Tool
An anonymous email is more than a free web service you visit. It is a fundamental component of digital hygiene and personal sovereignty. In an age where our data is the commodity, the ability to interact online without creating a permanent, searchable, and monetized record of our identity is not just convenient—it is essential for freedom of thought, association, and expression.
However, this power comes with a proportional responsibility. Using these tools without understanding their limits creates a dangerous illusion of safety. Using them for unethical or illegal purposes weaponizes a privacy tool and undermines the very reasons for its existence. The goal is not to hide from accountability, but to prevent unwarranted surveillance, data exploitation, and the chilling effect that comes from knowing every click is tracked.
Start small. Use a disposable service for your next newsletter sign-up. Experience the relief of an inbox that doesn’t belong to you. Then, if your needs grow, invest time in learning about and switching to a secure provider like ProtonMail, always pairing it with a trusted VPN. Treat your anonymous identity with the same care you would your physical safety: assess the risks, use the right equipment, and act with intention. In the digital world, your email address is often your front door. Sometimes, you need a key that doesn’t have your name engraved on it.
Frequently Asked Questions
Is using anonymous email completely untraceable?
No. It is not a magic invisibility cloak. Your anonymity depends on your practices. If you access it without a VPN from your home IP, your ISP and the email provider can see that connection. The goal is to sever the link between your *identity* and your *online activity*, not to become technically invisible to all observers. Using a VPN, Tor, and not revealing personal details in emails is essential for strong anonymity.
Can I send attachments with an anonymous email?
Usually, but with severe limitations. Most disposable email services block attachments entirely to prevent abuse. Secure providers like ProtonMail allow attachments, but they are encrypted. However, you must be extremely cautious: file metadata (like camera info in photos or author names in documents) can reveal your identity. Always scrub metadata before sending any file through an anonymous channel.
Will emails from an anonymous service be delivered to the recipient’s inbox?
Often, they will not. Domains used by temporary and anonymous email services have poor sender reputations because they are frequently abused for spam. As a result, major email providers (Gmail, Outlook, Yahoo) aggressively filter messages from these domains into the spam folder. The recipient may never see your message unless they manually check their spam folder.
Is it legal to create an anonymous email account?
Yes, in most countries, creating an account with a service that does not require your real name is legal. The legality is determined by how you use the account, not by its anonymous nature. Using it for legitimate privacy protection is legal. Using it to send threats, commit fraud, or engage in harassment is illegal, regardless of the email address used.
What’s the difference between a disposable email and a secure anonymous email?
A disposable email (e.g., 10MinuteMail) is a temporary, public inbox meant for one-time use. It requires no account and expires quickly. A secure anonymous email (e.g., ProtonMail) requires creating a persistent account (often without personal info) and is built with encryption and privacy laws to protect your long-term correspondence. Disposable is for avoiding spam on a single site; secure is for ongoing, private communication.
Can law enforcement trace an anonymous email?
They can try, and sometimes succeed. Their success depends on the provider’s logging policy and jurisdiction. A reputable provider in a strong privacy jurisdiction (like Switzerland) will fight legal requests and may not have the logs to comply. However, if you accessed your account without a VPN, your ISP has a record. If you used the email to commit a serious crime, providers will comply with valid international warrants. Anonymity raises the cost and difficulty of tracing, but does not guarantee it.